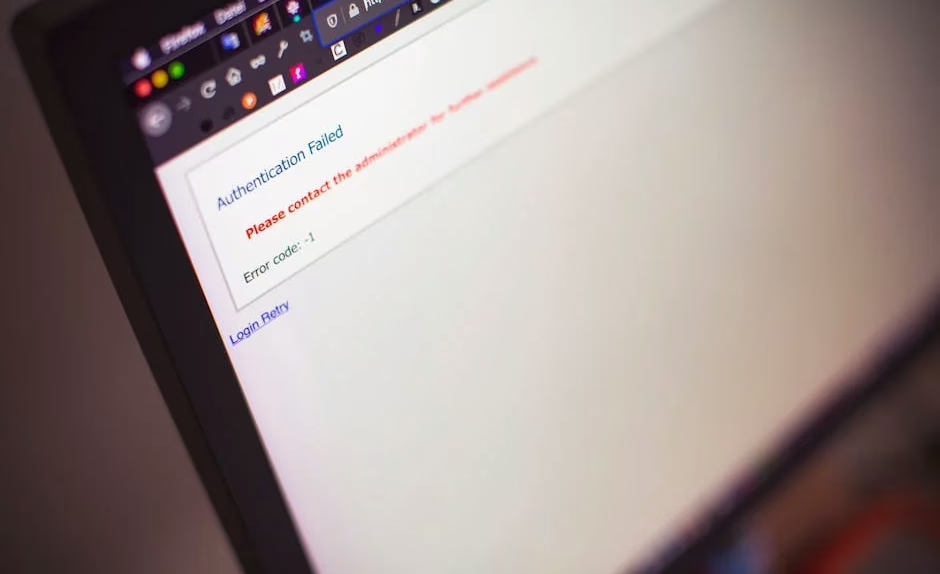
A critical authentication bypass vulnerability in cPanel & WHM has been exploited as a zero-day since February 23, 2026, affecting approximately 1.5 million internet-accessible instances worldwide. CVE-2026-41940 carries a CVSS score of 9.8 and allows remote, unauthenticated attackers to gain administrative access to web hosting control panels.
According to SecurityWeek, cPanel disclosed the vulnerability on April 28, urging immediate patching across all software versions after 11.40. The flaw affects the login flow and could lead to complete system takeover on shared hosting servers.
Technical Details and Attack Vector
The vulnerability exploits cPanel’s session handling mechanism during failed login attempts. WatchTowr Labs discovered that the cPanel service daemon writes pre-authentication session files to disk, which attackers can manipulate through specially crafted cookies.
The attack works by injecting specific characters via an authorization header to write attacker-controlled credentials in plaintext to the session file. Attackers then trigger a reload of this file to authenticate using the injected credentials, bypassing normal authentication entirely.
Rapid7 researchers noted that successful exploitation grants “control over the cPanel host system, its configurations and databases, and websites it manages.” This level of access enables attackers to modify server configurations and potentially compromise all websites on shared hosting infrastructure.
Zero-Day Exploitation Timeline
KnownHost CEO Daniel Pearson confirmed on Reddit that the vulnerability has been actively exploited since at least February 23, 2026 — more than two months before public disclosure. The hosting provider detected approximately 30 servers showing signs of attempted exploitation.
Dark Reading reported that multiple proof-of-concept exploits appeared within 24 hours of disclosure, with Censys Internet scanning showing attacks from multiple threat actors immediately following the April 28 announcement.
Major hosting providers including KnownHost, HostPapa, InMotion, and Namecheap implemented emergency access blocks to cPanel & WHM interfaces immediately after notification.
Additional Critical Vulnerabilities
LiteLLM SQL Injection Exploited
A separate critical vulnerability in the open-source AI gateway LiteLLM was exploited within 36 hours of disclosure. CVE-2026-42208 carries a CVSS score of 9.3 and involves SQL injection during proxy API key verification.
Sysdig researchers observed attackers targeting three database tables containing API keys, provider credentials, and environment configurations. The attacks occurred 21 minutes apart using automated tools with rotating IP addresses, though no credential abuse was detected.
Linux ‘Copy Fail’ Kernel Vulnerability
CVE-2026-31431, dubbed “Copy Fail,” affects Linux kernels since 2017 and allows authenticated attackers to escalate privileges to root. CISA added the vulnerability to its Known Exploited Vulnerabilities catalog, requiring federal agencies to patch within two weeks.
Microsoft reported limited exploitation primarily involving proof-of-concept testing, but warned of the vulnerability’s “broad applicability” and potential for container breakout and lateral movement in cloud environments.
Android Remote Code Execution
Google patched CVE-2026-0073, a critical remote code execution vulnerability in Android’s System component affecting the Android Debug Bridge daemon (adbd). The flaw allows code execution as the shell user without additional privileges or user interaction.
What This Means
The cPanel zero-day represents a significant supply chain security incident, given the platform’s widespread use across web hosting infrastructure. With 1.5 million potentially vulnerable instances and confirmed exploitation dating back months, the attack surface is substantial.
The rapid exploitation of newly disclosed vulnerabilities — particularly the 36-hour window for LiteLLM and 24-hour window for cPanel post-disclosure — demonstrates increasingly sophisticated threat actor capabilities and monitoring of security advisories.
Organizations using affected platforms should prioritize immediate patching and implement additional monitoring for signs of compromise, particularly focusing on administrative access patterns and configuration changes that could indicate successful exploitation.
FAQ
How can I check if my cPanel instance is vulnerable?
All cPanel & WHM versions after 11.40 are affected by CVE-2026-41940. Check your version in the cPanel interface and apply the April 28 security update immediately if you haven’t already.
What should I do if I suspect my server was compromised?
Look for unauthorized administrative access, unexpected configuration changes, or new user accounts created since February 2026. Consider rotating all administrative credentials and conducting a full security audit of hosted websites.
Are there any workarounds if patching isn’t immediately possible?
Several hosting providers implemented emergency access blocks to cPanel interfaces. Consider restricting cPanel access to specific IP addresses or implementing additional authentication layers as temporary measures while preparing for patching.