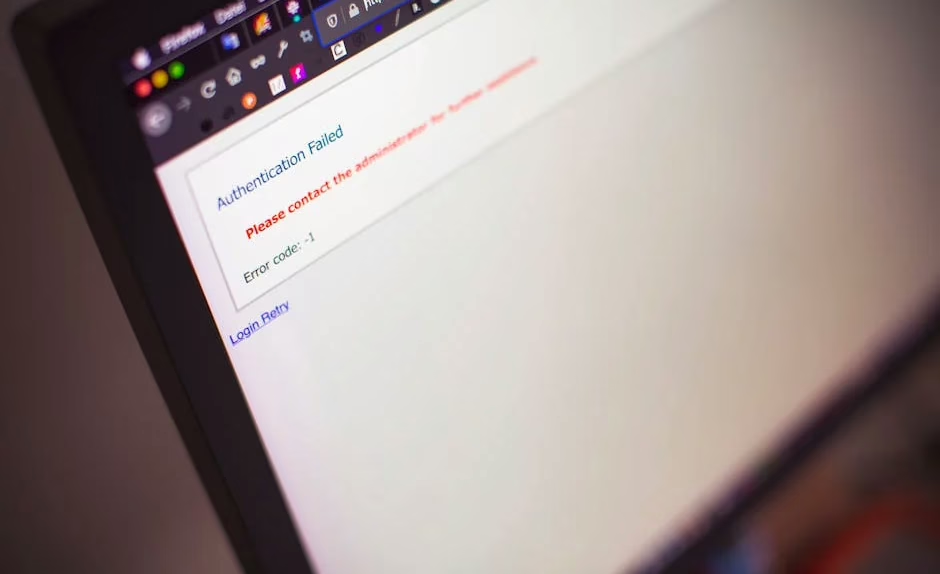
A critical authentication bypass vulnerability in cPanel & WHM has been actively exploited by attackers since February 2026, three months before its public disclosure on April 28. CVE-2026-41940, with a CVSS score of 9.8, affects all cPanel software versions after 11.40 and allows remote, unauthenticated attackers to gain administrative access to control panels.
According to SecurityWeek, the vulnerability impacts the login flow and could lead to complete system takeover. The Canadian Centre for Cyber Security warns that successful exploitation allows attackers to modify server configurations and potentially compromise all websites on shared hosting servers.
Vulnerability Details and Attack Method
Researchers at WatchTowr discovered that CVE-2026-41940 exploits a flaw in how cPanel handles failed login attempts. Upon a failed login, the cPanel service daemon writes a pre-authentication session file to disk, which attackers can manipulate through specially crafted cookies.
The attack works by injecting specific characters via an authorization header to write attacker-controlled credentials to the session file in plaintext. Attackers then trigger a reload of the file to authenticate using the injected credentials, effectively bypassing normal authentication mechanisms.
Rapid7 notes that successful exploitation grants attackers “control over the cPanel host system, its configurations and databases, and websites it manages.” A Shodan search reveals approximately 1.5 million internet-accessible cPanel instances potentially exposed to these attacks.
Timeline of Exploitation and Response
KnownHost revealed on Reddit that the vulnerability had been exploited in the wild since February 23, 2026 — more than two months before public disclosure. The hosting provider reported approximately 30 servers showing signs of attempted exploitation.
The vulnerability timeline unfolded rapidly after disclosure:
- April 28: cPanel issued security update and disclosure
- April 29: CVE-2026-41940 assigned with CVSS 9.8 score
- April 29: WatchTowr Labs published proof-of-concept exploit
- Within 24 hours: Multiple threat actors began exploitation attempts
Censys scanning data shows the vulnerability came under attack from multiple threat actors within 24 hours of public disclosure, demonstrating how quickly attackers can weaponize newly disclosed flaws.
Industry Impact and Hosting Provider Response
Major hosting providers moved quickly to protect their infrastructure after being notified of the vulnerability. KnownHost, HostPapa, InMotion, and Namecheap immediately blocked access to cPanel & WHM interfaces while applying patches.
The vulnerability poses particular risks for shared hosting environments, where a single compromised cPanel instance can affect multiple customer websites. Dark Reading reports that the flaw puts “millions of websites at risk via tens of thousands of compromised instances.”
KnownHost CEO Daniel Pearson confirmed in follow-up Reddit posts that exploitation had been ongoing “for at least the last 30 days,” with attack attempts dating back to February 23. This extended exploitation period highlights the challenge of detecting sophisticated authentication bypass attacks.
Additional Critical Vulnerabilities This Week
Several other critical vulnerabilities have emerged alongside the cPanel flaw:
LiteLLM SQL Injection (CVE-2026-42208): A critical SQL injection vulnerability in the open-source AI gateway LiteLLM was exploited just 36 hours after being indexed in GitHub’s advisory database on April 24. Sysdig reports that attackers specifically targeted database tables containing API keys and provider credentials.
Linux Copy Fail (CVE-2026-31431): CISA added this decade-old Linux kernel vulnerability to its Known Exploited Vulnerabilities catalog. The flaw affects all Linux distributions since 2017 and allows privilege escalation to root access.
Android RCE (CVE-2026-0073): Google patched a critical remote code execution vulnerability in Android’s System component that affects the Android Debug Bridge daemon (adbd).
What This Means
The cPanel vulnerability represents a significant supply chain security risk, given the platform’s widespread use across hosting providers worldwide. The three-month exploitation window before disclosure demonstrates sophisticated threat actors’ ability to discover and weaponize zero-day vulnerabilities in critical infrastructure.
Organizations using cPanel should prioritize immediate patching, as the combination of high CVSS score, active exploitation, and publicly available proof-of-concept code creates an extremely dangerous threat landscape. The rapid post-disclosure exploitation across multiple threat actors suggests this vulnerability will remain a high-value target.
The clustering of multiple critical vulnerabilities this week — spanning web hosting, AI infrastructure, operating systems, and mobile platforms — underscores the importance of comprehensive vulnerability management programs that can rapidly assess and respond to emerging threats across diverse technology stacks.
FAQ
What makes CVE-2026-41940 particularly dangerous?
The vulnerability allows completely unauthenticated remote attackers to gain full administrative access to cPanel instances, affecting approximately 1.5 million internet-accessible systems. Its exploitation since February 2026, months before disclosure, demonstrates active use by sophisticated threat actors.
How can organizations protect against this vulnerability?
Immediate patching of all cPanel & WHM installations is critical. Organizations should also implement network segmentation to limit access to cPanel interfaces, monitor for unusual authentication patterns, and consider temporarily blocking external access to control panels while patches are applied.
Why are we seeing multiple critical vulnerabilities disclosed simultaneously?
This appears coincidental rather than coordinated. The timing reflects normal security research cycles and responsible disclosure practices, though the concentration of high-severity flaws across different platforms creates an elevated risk environment requiring prioritized patch management.